![Cyber Authentication – Google Weak on Password Management Systems]()
by Dovell Bonnett | Dec 13, 2012 | Cloud Security, Cyber Security, Cyber Warfare, Data Security, Identity Theft, Multifactor Authentication,, Online Security, Password Authentication, Password Management, Social Networking
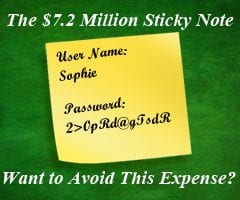
When it comes to cyber authentication, the weakest link is the user. Cyber authentication is a hot topic in today’s world of Malware, Cyber Warfare, BYOD, Cloud Computing and Hackers. In a recent Google Password Management blog, “Google Password Management Tips...

by Dovell Bonnett | Dec 2, 2012 | Cloud Security, Cyber Security, Cyber Warfare, Data Security, Multifactor Authentication,, Password Authentication, Password Management
Cyber Security begins with Network Access Authentication My first Law of Computers took a step backwards on November 20, 2012 with the announcement of the Pentagon’s new Cyber Warfare Central proposed by DARPA, Code Name “PlanX”. The Pentagon is giving birth to a...

by Dovell Bonnett | Nov 28, 2012 | Cloud Security, Cyber Security, Cyber Warfare, Data Security, Identity Theft, Multifactor Authentication,, Online Security, Password Authentication, Password Management
Network Access Authentication is essential to the Laws of Computers The concept of mechanical devices that will do manual and menial labor can be traced back to Ancient Greece. Whether it’s an automaton by Hephaestus or Honda’s Asimo robot, they all have something in...

by Dovell Bonnett | Sep 30, 2012 | Cyber Security, Data Security, Healthcare, Identity Theft, Online Security, Password Management
Using the Same Security Products! Ingersoll Rand Security Technologies provides high-quality reader and credential products to customers in both the physical and logical access control markets. All Ingersoll Rand readers and credentials are built on open standards,...

by Dovell Bonnett | Sep 21, 2012 | Cloud Security, Cyber Security, Cyber Warfare, Data Security, Data Theft Prevention, Healthcare, Hospital Information System, Identity Theft, Industrial Espionage, Multifactor Authentication,, Online Security, Password Authentication, Password Management, Power LogOn, Smartcards
Access Smart received their ECCN classification determination number today from the US Dept. of Commerce. We are classified as a 5D992b Information Security Software product which allows Access Smart to ship our Power LogOn software and licenses internationally. Under...

by Dovell Bonnett | Sep 6, 2012 | Cloud Security, Cyber Security, Cyber Warfare, Data Security, Data Theft Prevention, Healthcare, Hospital Information System, Identity Theft, Multifactor Authentication,, Online Security, Password Authentication, Password Management
Ingersoll Rand Security Technologies / Access Smart Provide Cyber Security with Smart Cards Affordable, smartcard based, enterprise password manager for Windows solution for network access authentication CARMEL, Ind – Sept. 6, 2012 – Ingersoll Rand Security...